One of the responsibilities of the Technical Coordinator in the Ohio Section is to submit something for the Section Journal. The Section Journal covers Amateur Radio related things happening in and around the ARRL Ohio Section. It is published by the Section Manager Tom – WB8LCD and articles are submitted by cabinet members.
Once my article is published in the Journal, I will also make it available on my site with a link to the published edition.
You can receive the Journal and other Ohio Section news by joining the mailing list Tom has setup. You do not need to be a member of the ARRL, Ohio Section, or even a ham to join the mailing list. Please sign up!
If you are an ARRL member and reside in the Ohio Section, update your mailing preferences to receive Ohio Section news in your inbox. Those residing outside the section will need to use the mailing list link above.
Updating your ARRL profile will deliver news from the section where you reside (if the leadership chooses to use this method).
Go to www.arrl.org and logon.
Click Edit your Profile.
You will be taken to the Edit Your Profile page. On the first tab Edit Info, verify your Email address is correct.
Click the Edit Email Subscriptions tab.
Check the News and information from your Division Director and Section Manager box.
Click Save.
Now without further ado…
Read the full edition at:
THE TECHNICAL COORDINATOR
Jeff Kopcak – TC
k8jtk@arrl.net
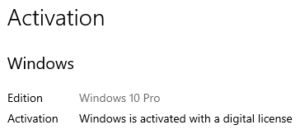
Coming soon: Windows 11. Wait, wasn’t Windows 10 the “last version of Windows?” Yes. Now, no. People interpret that statement to mean once you’ve upgrade to Windows 10, there would be free upgrades forever and you would never have to pay for another version of Windows. Microsoft: we kind of meant that but not really, it’s only “reflective” of delivery in an ongoing manner. On June 24th, Microsoft announced its next major version of the Windows operating system expected for release later in 2021.
As of this writing, no official release date has been set. Though a retirement date for Windows 10 in 2025 has been published. Retiring (or end-of-life) means after 10/14/2015, no mainstream support will be available for security updates, fixes, and enhancements. Businesses, or those paying for extended support. will likely have updates available for some time longer. The 2025 date puts Windows 10 in at over 10 years of service life, just a few months short of Windows 7’s service life. Has Windows 10 been out that long??
Microsoft is nothing, if not clear, in their statements and announcements. In Microsoft fashion, there is plenty of confusion around system requirements. Microsoft states that more than half, as much as 60%, of the PCs running Windows 10 today could not run Windows 11. I figure many systems upgraded from Win 7 to 10 will not meet the minimum requirements. Those who’ve bought a packaged PC since July 2016 should be good to upgrade and can upgrade for free. The reason for July of 2016 is when Microsoft required system integrators to include the TPM in new systems shipped after that date. TPM is used to generate cryptographic keys ensuring system integrity and security at system boot. DIY motherboards had this built in since about 2015. New PCs will see Windows 11 included as part of the entire purchase price. System builders will likely see the same prices as Windows 10, about $100 for Home and a little more for the Pro edition.
Home version of Windows 11 will require an Internet connection and a Microsoft account to complete first-time setup. If you have an account for Hotmail, Outlook, OneDrive, Office, or Xbox – you’re all set. If not, one can be created for free. Though nothing says you can’t unlink the account after setup. This connection between Windows and a Microsoft account has been used to store license information and retrieve a license should, when, a reinstall is needed. It also enables “cloud” features allowing some settings and preferences to be synced across all devices logged in with the same account. Pro versions can opt to use a Microsoft account or create a local account.
What else is new in Windows 11? “Sweeping” redesign of the user interface – to make it look more like a Mac – starting with a center aligned taskbar. A design choice aimed at touch users (tablets, Microsoft Surface devices). To be fair, GNOME has long adopted the center aligned taskbar as well as the Mac. Another start menu redesign “powered by the cloud” – which allows internet searches directly and synced documents across devices running Office 365. Microsoft Teams is directly integrated. Teams is the messaging and collaboration platform that started out as MSN Messenger and later absorbed Skype. To gain traction for the Windows Store (which no one ever went into), Windows will now be able to run Android apps natively.
Before the Microsoft announcement, a leaked build of Windows 11 appeared on the Interwebs. It appeared to be locked down to virtual machines only. Those that obtained the leaked version had significant issues installing it on bare metal. Not even an issue installing it on a virtual machine. The build might have been locked down to virtual machines for testing and demonstration purposes.

Since the announcement, a downloadable ISO image is still not available. There are guides how to download all the necessary files and build one yourself if you so choose to test out the preview on a real machine with a clean install. The official way is to enroll in the Insider program and do an in-place upgrade on a Windows 10 machine. This is done by signing into a Microsoft account in Windows 10, register for the Insider program online, enroll the device in the settings pane, then change Insider settings to the “Dev Channel.”
Though reviews have been initially positive about the new release, it seems very much like Windows 10 under the hood with the user interface redesign and improvements. Videos I saw had very good experiences gaming on the preview build leading more credence to it being Windows 10 underneath. If you’re like me and didn’t enjoy the user experience of having things buried, needing to do more clicks to accomplish the same/simple tasks, and ultimately moving to Linux as a result of Windows 10, this is going to be a ‘meh’ release for you as well.
On the subject of Windows. While I run Linux primarily and rag on current versions of Windows, if you are still running Windows 7 (which I am) or even XP on your machines, this is another friendly reminder to remediate, remove, or update unsupported versions of Windows. Removing would be replacing the machine or upgrade to a supported version of Windows if available. Remediate would be to remove Internet access to that device and remove its ability to access other devices on the Local Area Network by properly segmenting the device. Use of a hardware firewall appliance to block and monitor device communications is preferred. Should those options be unavailable, look to invest in a reputable service that provides patches for legacy operating systems such as 0patch (pronounced “zero patch”). 0patch Pro for Windows 7 end-of-support patching is available for 22.95 EUR +tax/computer (agent)/year, about $27 USD.
Vulnerabilities, such as PrintNightmare, will continue to be discovered. In situations such as this, emergency patches will be graciously released by Microsoft for unsupported operating systems but don’t expect this to continue. Vulnerabilities like this have always existed in affected operating systems but were only recently disclosed. PrintNightmare is a vulnerability in the Windows print driver, of all things. It allows a bad guy that has or can gain low level access to any affected Windows machine to take control of the local machine or domain controller gaining control of the entire domain. That second part regarding domains is not applicable to average users, only power users and corporations. Not to be out done by the exploit Microsoft botched the initial patch leaving systems still vulnerable. You would think a company worth $2 trillion would have the resources to fix the issue in its entirety.
Linux is not getting out unscathed this month too. I’ve talked about how I moved to Fedora and their very aggressive end-of-life cycle. Fedora 34 was released at the end of April. Typically, I’ll wait two months or so to let the bugs get sorted out in this community supported operating system. Realizing it had been three months since release, I took the dive and upgraded all my Fedora systems at once. Bad decision. I had two initial problems. My RAID array is showing individual disks in file explorer. This is a problem because it should never show individual disks. More to the point, if I accidentally write to an individual disk instead of the array because all elements are labeled the same (only the icon is different), the disk becomes out of sync with the rest of the array which would almost certainly result in data loss. The second is Redshift (shifts the screen color to red as it becomes later in the day to reduce eye strain) which keeps throwing an error at logon that all of a sudden manifested itself… from 2016. What? It’s been about an issue per day I’m discovering. Applications disappearing from the task bar is another very annoying issue. A downgrade attempt failed on the laptop which means wiping the operating system partition and re-installing Fedora 33. /home is on a separate partition meaning my files and most settings would be OK. Then praying 35 is not such a dud.
The Section is sponsoring learning and exploring sessions. Technical Specialist Jason – N8EI will be presenting one of those sessions on August 31st. Look for details in this edition or in forthcoming communications from our Section Manager. His topic is “Beyond the Baofeng: Thoughts on Equipment Choices for New Hams.” You received your license. Picked up a $20 Baofeng. Tried to reach some repeaters with it. Now what? Now comes a real station. He touches on prioritizing equipment purchases and gives recommendations on radios. It will be a good one not only for newly licensed hams but hams looking to improve their station.

I’m jiddy that Hamfests are returning. I made both NOARSFest in Elyria and the Van Wert Hamfest last weekend. NOARSFest seemed like a few more were in attendance over previous years. That was the last hamfest I attended before we were sequestered to our homes so it was fitting being the first one to return. Van Wert had a perfect day for holding a hamfest – though it was quire foggy on the ride out, maybe due to the wildfires out west. Even though I attended school in the area and traveled often for work, never made it to Van Wert. Their ‘fest was one I’ve been wanting to attend for some time. Figured I would take in all that I can and support hamfests as much as I can this year seeing as all were canceled leaving clubs without that income over the last year.
Thanks for reading and 73… de Jeff – K8JTK