One of the responsibilities of the Technical Coordinator in the Ohio Section is to submit something for the Section Journal. The Section Journal covers Amateur Radio related things happening in and around the ARRL Ohio Section. It is published by the Section Manager Tom – WB8LCD and articles are submitted by cabinet members.
Once my article is published in the Journal, I will also make it available on my site with a link to the published edition.
You can receive the Journal and other Ohio Section news by joining the mailing list Tom has setup. You do not need to be a member of the ARRL, Ohio Section, or even a ham to join the mailing list. Please sign up!
If you are an ARRL member and reside in the Ohio Section, update your mailing preferences to receive Ohio Section news in your inbox. Those residing outside the Ohio section will need to use the mailing list link above. Updating your ARRL profile will deliver news from the section where you reside (if the leadership chooses to use this method).
- Go to www.arrl.org and click the Login button.
- Login
- When logged in successfully, it will say “Hello <Name>” in place of the Login button where <Name> is your name. Click your Name. This will take you to the “My Account” page.
- On the left hand side, under the “Communication” heading (second from the bottom), click Opt In/Out
- To the right of the “Opt In/Out” heading, click Edit
- Check the box next to “Division and Section News.” If it is already checked, you are already receiving the Ohio Section Journal.
- Click Save
- There should now be a green check mark next to “Division and Section News.” You’re all set!
Now without further ado…
Read the full edition at:
THE TECHNICAL COORDINATOR
Jeff Kopcak – TC
k8jtk@arrl.net
Seven operators activated Special Event Station W8B on July 16, 2022. Operating team consisted of: Technical Specialist Bob – K8MD – Bird employee and mastermind in planning the event, K8FH – Fred, K8TV – Ken, KC8NZJ – Mat, NF8O – Dave, KE8BKI – Stephanie, and K8JTK. This Special Event commemorated 80 years of Bird Electronic Corporation and 70 years of the Model 43 Wattmeter.
In 1940, J. Raymond Bird developed a way to quickly and accurately measure forward and reflected power in coax transmission lines. In April 1942, Bird Engineering Company was founded in Cleveland, Ohio. According to an old sign on their website, the original location was on E. 38th street. Later, the company renamed to Bird Electronics Corporation. After securing important contracts in the late 1950’s, they located to their current facility in Solon, Ohio. Bird was instrumental in the Mercury and Apollo space programs during the 1960’s, supplying radio-tracking equipment and loads for equipment testing. Today, Bird manufactures and packages test equipment, signal boosters, analyzers, and recording equipment.

In 1953, the Bird 43 RF Wattmeter was introduced and quickly became the industry-standard tool for RF power measurement. A staple in many ham shacks, the Bird 43 is popular in commercial and broadcast industries as well. During the 1970’s, Bird provided critical and affordable test equipment to ham radio operators during emergencies which helped Bird become a household name. The 43 is popular because it can measure a wide range of frequencies, 450 kHz to 2.7 GHz between 100 mW to 10 kW, using plug-in elements. These elements are commonly referred to as “slugs.” The meter is an insertion-type, meaning placed in-line of the transmission line, measuring forward and reflected power.
Started out as a dreary, rainy morning. When I left my QTH, the sun was starting to make an appearance. Rain held off for us to operate 7 hours before another round was on its way. Three portable stations were operational. Two HF by K8MD and K8FH, and one VHF/UHF by K8TV. The HF antennas were portable turnstile dipoles with a fabricated or Spiderbeam center mast. These are quickly deployable and go up in about 20 minutes. The VHF/UHF was a commercial antenna on a fabricated mast that rose just above one of the unloading docks.

Plan was to be on the air by 1000 local. Setup went quick and W8B was operational around 0900 testing the equipment with a few initial contacts. We operated from the outdoor employee patio of Bird. Operators were treated to a tour of the factory by K8MD. It was nothing short of impressive. In order to test manufactured products, there are high power broadcast transmitters for dummy load testing and plenty of test equipment that any ham would love to have in their shack. Most products, including the 43, are made, tested, and shipped from the Solon, Ohio location.

After the tour, we met executives Katie Wright – Director of Strategic Development, Dana Svilar – Manager of Marketing Communications, and CEO Terry Grant. They were interested to see the setup and how the event was progressing. We explained and demonstrated the digital station. Sideband contacts were made and they heard from hams that own a Bird 43.
The bands weren’t the best to start out. On 40m, we’re logging contacts. Then, like a light-switch, there was nothing, including on FT8. Katie was trying to coordinate a contact with N1KSC, Kennedy Space Center Amateur Radio Club, with some close friends of hers. For a good while, they were hearing us 59 but we did not copy them at all. Right about noon, K8MD finally established contact. There was still plenty of QSB but he got them in the log. Katie even got on the radio to say a few words during the exchange!
K8TV operated the VHF/UHF station. He was making contacts on repeaters in Lorain (close to 40 miles at our 1100 ft elevation) and surrounding counties, including making simplex contacts. K8FH operated the CW station. NF8O made quite a number of sideband contacts in the afternoon despite the up-and-down band conditions. K8MD, KC8NZJ, and myself operated FT8 throughout the day.
Bird graciously bought us lunch from a local pizzeria and we received swag for coming out and playing radio. We operated until 1600, a little past that on the digital station, and started to strike the equipment. We were on the road home around 1700.
164 contacts were made: CW: 5, SSB: 37, FM: 26, FT8: 96. Thanks to K8MD who planned the event. Bird Electronic Corporation for allowing us to operate from their facility and their hospitality. If you made contact with W8B, you will receive a QSL card, designed by Dana, as a thank you.

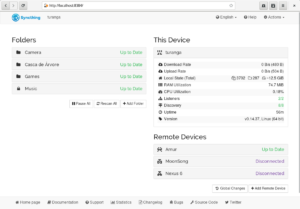
One of the many things on my ham radio “do-more-with” list is AREDN mesh. I have a MikroTik RouterBOARD hAP ac lite node I setup some time ago. I haven’t done much with it due to not having any real way to get a high-profile node and no other nodes are around me. It’s been running in the shack with a tunnel to W8ERW & Sandusky ARES. I haven’t advanced much on “now what?” after the initial exercise of flashing a node with AREDN’s firmware.
If you have an AREDN node and haven’t updated in the last few months, start planning an upgrade. AREDN implemented many projects which have made considerable improvements to the firmware. The original Broadband-Hamnet was written in Perl and AREDN continued to build on and maintain Perl code. A conversion from Perl to the Lua programming language has been completed. This conversion recovered a lot of memory by removing large Perl libraries. Nodes will now run code optimized for embedded devices. Memory saved by the conversion means the tunnel package and iperf3 (speed testing) are now bundled with the base firmware. Previously, both had to be installed manually after each upgrade.
Upgrades and selecting the correct firmware should be much easier too. Nightly builds are available for testing new features or tweaks in the firmware. Though, “nightlies” as they are called, are pre-alpha releases. According to the project, theirs are pretty stable. This doesn’t mean they should be installed on production nodes in hard-to-reach places in case something goes sideways.
Link Quality Management has been added to help optimize networks and drop links that cause network problems. Nodes with poor SNR, too far away, or prone to many retransmissions can be dropped automatically. These cause poor performance for nodes without those issues. An example: a high-profile node has to account for all connected nodes. If a node 40 miles away from its location its connected, it must wait for acknowledgments from all connected nodes. Should that node 40 miles away not be able to receive messages or messages can’t be delivered back to the high-profile node, this degrades speed and performance significantly. The high-profile node must wait for responses and possibly keep retransmitting the same message to that node until a response is received. LQM will drop nodes that do not meet quality criteria. This feature is turned off by default, unless it was configured previously.
These updates, network design basics, and demo of the next generation user interface are covered in a recent LAXNORTHEAST meeting. That meeting is available on YouTube featuring AREDN representative Orv – W6BI. He deployed the mesh backbone in Ventura and western Los Angeles Counties. His presentation isn’t introductory but is beneficial for those who have setup and maintain a node.
A radio that covers ALL ham radio voice digital modes? Reality or vaporware? Projects, like the DV4 Mobile, have been vaporware. Taking a swing at the market this time is the Connect Systems CS800D PLUS. It claims: to store 520,000 contacts and 64,000 channels, have the ability to do DMR, FUSION, DSTAR, P25 and NXDN, make its own code plug on the fly, and many more features yet to come. Consider me intrigued. OK, it doesn’t do most of this out-of-the-box. Essentially the CS800D PLUS is the CS800D today, a DMR and analog dual-band mobile radio. Features will be added ‘without the manufacture’s cooperation’ and ‘firmware will be done by the Amateur community.’ Not really sure how that is going to work since the existing firmware isn’t open sourced, documented, or have documented hooks/APIs. Additionally, the “all digital modes” comes via a “co-processor or your laptop to allow you to add digital modes not currently in the radio.”
I have the CS800D but purchased one of these anyway to see if this actually comes to fruition, especially the ‘all the digital modes’ part. If not, it or my 800D will appear on the used market! I envision this radio will utilize a NW Digital Radio DV3000 or DVMEGA DVstick on a Raspberry Pi or computer using a serial connection between the radio and computing device. This would provide off-radio encoding/decoding of digital modulation and analog frames. No working proof of concepts or documented working setups have been posted as of this writing. Posted documents mostly show how to convert codeplugs between the CS800D and CS800D PLUS. Firmware for the CS800D PLUS is not backwards comparable with a CS800D, according to Connect Systems. The CPS will work with both radios but the firmware is not compatible due to CPU and memory differences.

Flying under my radar was the release of the SharkRF openSPOT 4. After reading up, it’s another incremental release. What’s new in the 4? Improved battery life (up to 30 hours), multi-core CPU, new WiFi module, and split into two offerings: openSPOT 4 and openSPOT 4 Pro. That’s it, near as I can tell. It’s probably due to chip shortages, but the openSPOT 4 is available now where as the openSPOT 4 Pro is due to ship again August 20th.
What’s the difference between the 4 and 4 Pro? Hardware cross mode capability and price. The openSPOT 4 rings in a € 249.00 ($254.14 USD) and the 4 PRO at € 319.00 ($325.59 USD, both conversions as of this writing). First introduced in the openSPOT 3, SharkRF hotspots are the only ones with the ability to cross mode D-STAR with DMR, C4FM, and NXDN networks. The 4 does not have the capability to cross mode D-STAR with other networks, the 4 Pro does have this capability. As with other openSPOT releases, the release of the OS4 end-of-life’s the previous model. The openSPOT 3 will probably get some firmware updates here-and-there but don’t expect many more based on past experience. I liked the openSPOT 3 for what it was. The 4’s are another pass for me because this release that doesn’t offer much more features than my openSPOT 3.
Nearly as soon as the OSJ went to publish last month, the wording about DroidStar no longer being available for iOS was removed. It appears the issues of concern were resolved. DroidStar is back in TestFlight and I heard from iOS users that it was working for them again.
Thanks for reading and 73… de Jeff – K8JTK