One of the responsibilities of the Technical Coordinator in the Ohio Section is to submit something for the Section Journal. The Section Journal covers Amateur Radio related things happening in and around the ARRL Ohio Section. It is published by the Section Manager Scott – N8SY and articles are submitted by cabinet members.
Once my article is published in the Journal, I will also make it available on my site with a link to the published edition.
You can receive the Journal and other Ohio Section news by joining the mailing list Scott has setup. You do not need to be a member of the ARRL, Ohio Section, or even a ham to join the mailing list. Please sign up!
If you are an ARRL member and reside in the Ohio Section, update your mailing preferences to receive Ohio Section news in your inbox. Those residing outside the section will need to use the mailing list link above.
Updating your ARRL profile will deliver news from the section where you reside (if the leadership chooses to use this method).
Go to www.arrl.org and logon.
Click Edit your Profile.
You will be taken to the Edit Your Profile page. On the first tab Edit Info, verify your Email address is correct.
Click the Edit Email Subscriptions tab.
Check the News and information from your Division Director and Section Manager box.
Click Save.
Now without further ado…
Read the full edition at: http://arrl-ohio.org/news/OSJ-October-17.pdf
THE TECHNICAL COORDINATOR
Jeff Kopcak – TC
k8jtk@arrl.net
October is National Cyber Security Awareness Month. I either made your eyes roll because security can be complicated or piqued your interest because of the TWO Equifax breaches. I can certainly get into the weeds with data and cybersecurity because it’s an interest of mine – as a user and programmer. Realizing that most readers won’t have a background in programming or system administration, I’ll set aside the technical details. I’ll briefly cover some cybersecurity issues and give tips anyone reading this article can use.
The whole concept of computing is built on trust. The list of things we trust is infinitely long: trust programmers of the operating system and program developers are following good practices. Trust the company stands behind their product, fixing problems and issues. Trust “Information Security Officers” of a company actually have a background in information security. Trust audits are taking place to uncover problems. Trust customer data is being stored in accordance with good security practices. Trust the website you’re browsing to is really CompanyWebsite.com. Trust “[insert name of company here] Free Wi-Fi” is really that company’s free Wi-Fi. Trust that devices in your home aren’t spying on you. You start to get the idea.
Security is a tradeoff between safety and convenience. Computing could be made very secure but those systems would be completely unusable due to the layers of security. There is no such thing as a “completely secure” system or device – it just means the mistakes, problems, and bugs haven’t been found yet. “Shellshock” is considered to be a very severe security bug. Disclosure came in September of 2014. This bug affected millions of servers connected to the internet. It was determined the bug, in some form, had existed in the UNIX (and Linux) command-line interface since 1989.
Humans program computers. Humans use computers. Humans make mistakes.
Hackers leverage these mistakes and use them to their advantage, often to gain unauthorized access. The word “hacker” has two meanings. “White-hat hackers” are the ones who experiment with and modify devices and software to make it work better. Hams are examples of these because we take commercial gear and make repeaters or use off-the-shelf routers for things like Mesh networking. “Black-hat hackers” are the bad guys and the ones we hear about on the news stealing credit card data from Target and personal data from Equifax. These are the ones I will be referring to.
Hollywood gives us the perception that hackers are in some 3rd- world country or in a dark basement, no lights, and only the glow of their computer screens. Hackers come from all parts of the world and sometimes are acting on a government’s behalf. In fact, legitimate companies exist solely to sell their black-hat hacking tools. They have buildings, employees, call centers, and help desks – as does any legitimate company.
world country or in a dark basement, no lights, and only the glow of their computer screens. Hackers come from all parts of the world and sometimes are acting on a government’s behalf. In fact, legitimate companies exist solely to sell their black-hat hacking tools. They have buildings, employees, call centers, and help desks – as does any legitimate company.
What’s the motivation behind hacking?
Money. It’s hard not to tie everything back to money. The first reference to malicious hacking was “phreaking” (pronounced freaking. AKA: phone hacking) where one of the goals was to manipulate the public phone system and use it to make long-distance calls when it was very expensive to call around the world. More recent financial examples include everything from disrupting nation-states (economic), blackmail, and ransom payments for access to data. Ransomware encrypts all documents and pictures. It demands payment before it will (hopefully) decrypt your files allowing you to use those files again. Ransomware utilizes the same technology, strong encryption, which you use to securely transact with your bank online.
My social media, computer, or online account has no value [to me] / I only check email / I don’t store anything on my computer / why would anyone want access to my email or computer?
I hear these alot. Many of us don’t realize all the things a bad guy can do with computer access or an email account. Brian Krebs is a blogger who covers computing security and cybercrime on his website Krebs on Security. He is known for infiltrating underground cybercrime rings and writes about his experiences. His site is highly recommended reading for anyone with an interest in cybersecurity.
Brian posted two articles titled “The Value of a Hacked Email Account” and “The Scrap Value of a Hacked PC…” When signing up for any online service, an email address is almost always required. In 2013, according to Brian’s article, hackers who have access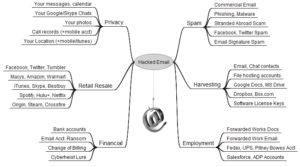 to email accounts can subsequently gain access to other services such as iTunes and sell that access for $8 each. FedEx, Continental, United accounts go for $6. Groupon, $5. Hosting and service accounts like GoDaddy, AT&T, Sprint, Verizon Wireless, and T-Mobile, $4 apiece. Facebook and Twitter accounts were $2.50/ea.
to email accounts can subsequently gain access to other services such as iTunes and sell that access for $8 each. FedEx, Continental, United accounts go for $6. Groupon, $5. Hosting and service accounts like GoDaddy, AT&T, Sprint, Verizon Wireless, and T-Mobile, $4 apiece. Facebook and Twitter accounts were $2.50/ea.
Aside from the monetary value, bad guys have access to family pictures, work documents, chat history, can change billing and deposit addresses on banking accounts, drain financials like 401K, bank or stock accounts, and target other individuals like family members. In 2012, a hacker went after Wired journalist Mat Honan locking him out of his digital life. The attacker used flaws in Amazon and Apple’s services, which helped them gain access to Mat’s Gmail and ultimately his Twitter account.
Access to a personal computer can be gained through a number of schemes including: fake ‘you have an out-of-date plugin/flash version’ on a webpage, receive an email about a past due invoice, notification of a problem with some shipment, or by innocently installing a program thought to be legitimate. A recent example of a compromised program was the widely popular PC maintenance program, CCleaner. Untold millions of people unknowingly downloaded a malicious version of the program from the vendor’s site.
 A hacked PC can be used for: generating email spam, harvesting other accounts (see above), gain access to a work network, steal online game keys and characters, be part of a Denial of Service attack, infect other devices on the network (like DVRs), create fake eBay auctions, host child porn, capture images from web-cams or network cameras and use them for extortion purposes.
A hacked PC can be used for: generating email spam, harvesting other accounts (see above), gain access to a work network, steal online game keys and characters, be part of a Denial of Service attack, infect other devices on the network (like DVRs), create fake eBay auctions, host child porn, capture images from web-cams or network cameras and use them for extortion purposes.
What can I do to protect myself?
Unfortunately in situations of compromise like Target and Equifax, there was nothing you could do – other than not use a credit card at Target or not apply for any kind of credit reported to Equifax. Unlikely for many. You can only react after-the-fact by closing accounts with fraudulent charges and place credit warnings or freezes on your credit.
The SANS Institute, which specializes in information security and cybersecurity training, offers a “monthly security awareness newsletter for everyone” called “Ouch!” Their October 2017 newsletter outlines five steps to help anyone overcome fears and securely use today’s technology. Check the newsletter for more information on these points.
- Social Engineering: is an old technique which creates a sense of urgency to tick people into giving up information they shouldn’t: someone needs money quickly, boss needs a password, the IRS is filing suit against you, Microsoft Tech Support calls you about a “virus” on your computer, etc. Never give a password, any personal information, or remote access to any solicitor.
- Passwords: Create unique, strong passwords for all online devices and online accounts. Use a password manager which will assist in creating strong passwords. LastPass utilizes a web interface and cloud storage, KeePass is an application and stores the database locally on your computer. Both are excellent solutions for a password manager.
If you’re uncomfortable with a password manager, use pass-phrases which are passwords made up of multiple words. Passphrases can be written down, but store these in a secure location. Use two-step verification, often called two-factor authentication. Two-factor authentication (2FA) is a combination of something you know (your password) and something you have (a smartphone). A list of services offering 2FA with instructions can be found at: twofactorauth.org. Note: text messages are NOT a secure two-factor method because the cellphone network is not secure and attackers have been able to re-route text messages. - Patches: Put all devices connected to the Internet behind a firewall (router) and keep all systems connected to the internet up-to-date. This includes home routers, computers, smartphones, tablets, streaming media devices, thermometers, Raspberry PIs, lights, automation systems, speakers, and video cameras. If devices are not being updated by the vendor, potentially dangerous mistakes are not being fixed. It’s time to consider better devices.
- Anti-virus: can protect you when you accidentally click on the thing you shouldn’t have and infected your system. It won’t protect against every form of infection. Windows Defender, available for all current Windows operating systems, is sufficient.
- Backups: I cannot stress this enough, backup, backup, backup! Many times I’m asked something similar to: ‘how can I recover my daughter’s wedding pictures from my computer’s crashed drive?’ Maybe you can, but often not. ‘I lost my phone, didn’t have cloud backup enabled, and had vacation pictures on there.’ Yea, they’re really gone. Backups serve as a way to recover from your own mistakes like accidentally deleted files and ransomware cyberattacks. A “3-2-1 backup strategy” includes 3 copies of your data, 2 on different media, 1 off-site. For most of us, this means: the original data is the 1st copy, an external hard drive (disconnected when not copying data) or network storage drive houses the 2nd copy, and a copy on a USB flash drive stored at work or backed up using a cloud backup solution – is the off-site 3rd copy.
A layered approach to security is considered best practice. As an example, creating strong passwords AND using two-factor authentication. The more layers the better, but more layers means less convenience. Brian Krebs also offers his “Tools for a Safer PC” which includes switching to OpenDNS in your home router. DNS is the service that turns human-readable URLs into IP address. OpenDNS blocks communication with known malware sites.
Hopefully this information has grabbed your attention and guided you to take steps to become safer online. Thanks for reading and 73… de Jeff – K8JTK
Imgs: Krebs on Security, Ars Technica.
